Cyber Deception Platforms – Honeypot Architecture and Working
Introduction
A Honeypot is a network-attached system used as a trap for cyber attackers/hackers. It is used to detect and study the tricks and types of attacks used by hackers. It acts as a potential target on the internet and informs the defenders about any unauthorized attempt at the Critical Information Infrastructure.
Honeypots are mostly used by organizations working in cybersecurity domain. It helps cybersecurity organizations and researchers to learn about the different types of attack techniques that attackers can use. Sometime it is also seen that even cybercriminals use these honeypots to decoy researchers and share the wrong information.
Honeypot Key Pointers
- A honeypot is a fake system designed to attract and monitors hackers
- It helps security teams to spot attacks quickly with fewer false alarms
- Honeypots can look like real websites, servers, or a login pages.
- Honeypots are deception based security systems
- Any interaction with a honeypot is considered high-confidence malicious activity.
- Honeypots can emulate services, operating systems, or full network environments.
- They are classified as low, medium, or high interaction based on realism and risk.
- Honeypots help analyze attacker TTPs means Tactics, Techniques, and Procedures aligned with MITRE ATT&CK.
- They are widely used to malware capture, exploit analysis, and threat intelligence generation.
- They can detect if a hacker is moving inside a network after breaking in.
- Overall, honeypots act like a trap that helps improve cybersecurity without risking real systems.
Honeypot System Architecture
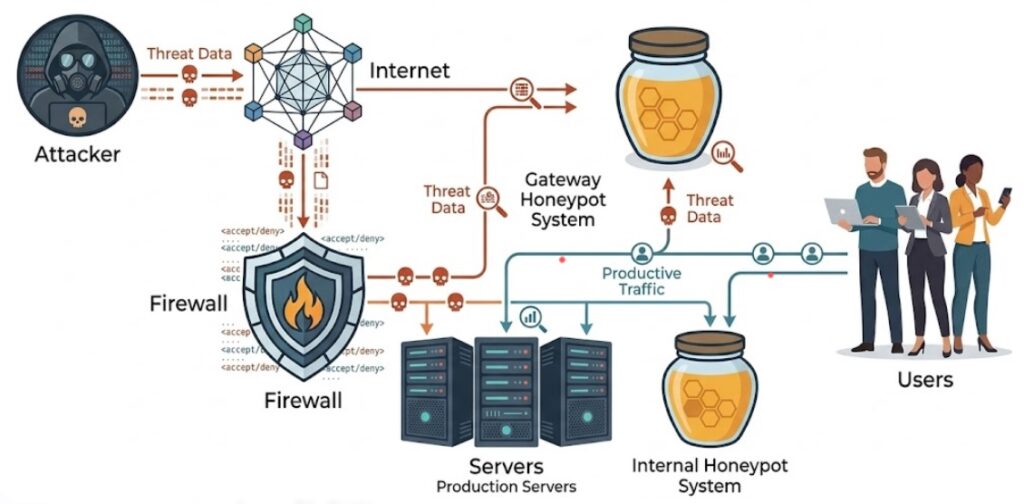
A Honeypot working architecture is shown in following picture.
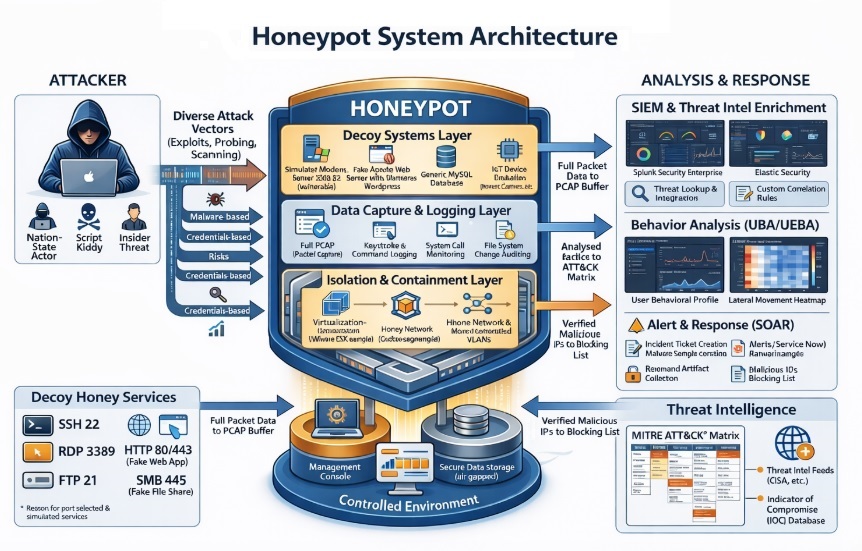
Decoy Systems Layer
The Decoy Systems Layer also known as Engagement Layer is the part of a honeypot that acts like a real system to attract attackers. It is consist of fake services such as web servers (HTTP/HTTPS), login services like SSH, FTP, and RDP, as well as simulated databases and even could have IoT devices. These systems are intentionally made to look vulnerable so that attackers interact with them, thinking they are real targets.
The main purpose of this layer is to safely trick attackers into revealing what they are doing e.g. scanning networks, trying to break in, or using stolen credentials. This helps security teams understand how attacks happen in real-world environments without putting actual systems at risk.
Data Capture & Logging Layer
The Data Capture & Logging Layer also referred as Monitoring Layer. It is the most important layer of any honeypot because it records everything an attacker does. It captures full network traffic (PCAP), logs each and every command or keystroke entered by the attacker, monitors system-level activities, and tracks any changes made to files.
This detailed recording by this layer helps security teams clearly see how an attack is performed, what tool or malware is used, and what steps/methods the attacker takes. The captured data is analyzed and investigated, to make it easier to understand threats and improve overall security defenses.
Isolation & Containment Layer
The Isolation & Containment Layer also called Security Layer. This layer makes sure that the honeypot stays safe and cannot be used by attackers to harm real systems. It uses systems like virtual machines, sandbox environments, and network segmentation to keep the honeypot completely separated from the main real network.
Even if an attacker runs malware inside the honeypot, it is remains within this controlled environment. This stops the attacker from moving to other systems and safeguard important infrastructure, while still allowing security teams to safely observe and study the attack patterns.
Analysis & Response Layer
In, Analysis & Response Layer all the collected data from the honeypot is studied and turned into actions. It connects with security tools like SIEM to gather and analyze logs in one place, helping detect suspicious activities and generate alerts. Behavior analytics (UEBA) is used to understand attacker patterns, track their movement within the system, and build behavior profiles.
At the same time, SOAR tools can automatically respond to threats by blocking malicious IPs, updating firewalls, or containing malware. This layer helps organizations quickly understand attacks and take the right actions to stop them.
Threat Intelligence Layer
In Threat Intelligence Layer, the raw data collected from attacks is converted into useful information that security teams can act on. It organizes attack details by mapping them to known techniques such as the MITRE ATT&CK framework, and combines this data with external threat intelligence feeds to get a bigger picture of ongoing threats.
This layer also identifies important warning signs, such as malicious IP addresses, domains, and other indicators of compromise (IOCs). This helps organizations quickly recognize similar attacks in the future and strengthen their overall security.
Management and Storage Layer
Management & Storage Layer is responsible for controlling the honeypot system and storing all the collected data safely. This layer can have a central dashboard where security teams can monitor the status and health of the honeypot, along with secure storage systems to protect sensitive data.
Visual dashboards help in understanding attack patterns and trends them over time. This layer ensures that all logs and evidence are stored securely and can be easily available anytime for analysis and future investigations.
Honeypot Deployment Models and Interaction Levels
Honeypots can be set up in different levels depending on how much interaction they allow with attackers.
- Low-interaction honeypots creates basic fake services like a simple SSH login screen just to detect and log quick attacks, making them easy and safe to use.
- Medium-interaction honeypots provides more realistic responses, allow attackers to do a bit deeper actions and help in capturing more detailed behavior without exposing a full system.
- High-interaction honeypots are the most advanced, using real operating systems and services to observe the complete attack methodology from entry point to data theft, but they require strong security controls like virtual machines and network isolation to prevent any real damage.
Deployment Strategies in Enterprise Environments
A honeypots deployment strategy depends the security needs of an enterprise. Some of most common strategies are listed below.
- DMZ-based honeypots are placed on internet facing networks to mimic public services and detect external attacks like scanning and exploitation attempts.
- Internal network honeypots are used the organization to detect suspicious activities such as lateral movement or insider threats from compromised systems.
- Cloud honeypots are deployed on platforms like AWS, Azure, or GCP to monitor risks such as API misuse and leaked credentials.
- In Distributed deception, multiple honeypots are placed across different network segments to closely resemble a real enterprise setup, making it easier to detect and analyze advanced, coordinated attacks
Advantages of Honeypots
- Honeypots provides valuable real-time attack data and insights
- They can detects malicious activity even in encrypted traffic
- Honeypots can diverts and wastes attackers’ time and resources
- It enhances overall security visibility and defense
Disadvantages of Honeypots
- Honeypots can be identified by skilled attackers
- It Detects only direct attacks so have limited visibility
- It can be misused if not properly secured
- Vulnerable to fingerprinting techniques
Conclusion
Honeypots help organizations move from just reacting to attacks to actively detecting and understanding them. By working with modern security tools, they give clear insights into how attackers behave. This helps in detecting threats faster, responding quickly, and improving overall security over time.
